Author: Lee McMillan, Director of Product Marketing
As cyberattacks continue to grow both in numbers and sophistication, establishing cybersecurity for infrastructure projects and organizations is more crucial than ever before. 2021 was a record-breaking year for cyberattacks, with malware increasing by 102% and experts estimating cybercrime will cost the world $10.5 trillion annually by 2025.
While all organizations are potentially vulnerable to cyberattacks, the infrastructure industry has become a common target—seeing a 34% increase from 2020 to 2021. Why? The largest contributing factor is that infrastructure companies tend to not prioritize upgrading their software systems. Deferred maintenance of software systems may seem to save time and money (and require no effort) in the short-term, but creates potential long-term complications and costs that far outweigh the momentary ease of sticking to the status quo. In fact, the longer these systems go without modernization, the more expensive they ultimately become to maintain.
This issue is not distinctly infrastructure-related: 70% of businesses do not complete their digital transformation plans. However, cybercriminals are aware that infrastructure companies are particularly hesitant to upgrade—and therefore they are frequent and appealing targets. A lack of employee training further compounds this issue: Employees are often not provided with the tools and knowledge to avoid exposing their organizations to even further risk.
One recent example of an infrastructure cyberattack was the April 2021 breach of the Colonial Pipeline Co.’s network. After accessing the network via compromised password, cybercriminals stole 100 gigabytes of data from Colonial Pipeline and threatened to leak the information if a cryptocurrency ransom was not paid. This ultimately led to a complete, precautionary shutdown of the entire pipeline—the first in its 57-year history.
Why are home-grown tech solutions so vulnerable to cybercrime?
Many government agencies rely on decades-old systems that are incapable of integrating with other systems. While they may be familiar and comfortable, they present significant risks. They frequently introduce a single point of failure and the vast majority of these legacy systems have not been updated with security measures to appropriately address modern day ransomware. As such, they are alluring targets for hackers and require less effort to breach.
Some agencies have developed internal software systems to counteract this issue—but this approach is ultimately more costly and inefficient than simply migrating to a modernized, cloud-based system. Internal software systems not only require a dedicated in-house staff for training and maintenance purposes, they lack the ability to evolve, integrate with other solutions, and ultimately, require additional management, reporting, and budgetary requirements.
What can owners do to protect large public infrastructure from cyber criminals?
Migration to a cloud-based system is key to both security and innovation. Infrastructure agencies can protect their data from cyber attacks by replacing legacy systems with modernized solutions. Doing so provides a multi-layered security approach that mitigates threats before they can become severe cyberattacks.
Infrastructure owners, specifically, stand to benefit immensely from adopting a cloud solution. Despite past hesitation to modernize, the needle is beginning to move: More and more organizations are coming to the conclusion that their legacy systems are not designed to handle the challenges of modern-day cyberattacks. This shift in perception has only gained further momentum due to the transition to remote work. In fact, a 2020 study determined that cloud services are becoming increasingly vital in modern, digital services delivery within the U.S. infrastructure industry.
How does modernizing technology help secure the data that is most vulnerable to cyber crime?
One key way to protect recover data lost from bad actors during a cyberattack is through cloud-based, modernized technology. HeadLight’s visual-based inspection technology for infrastructure projects allows teams to capture, share, and act on data from the jobsite in real time. This not only increases the accountability and effectiveness of construction projects—it can be instrumental in securing vulnerable data.
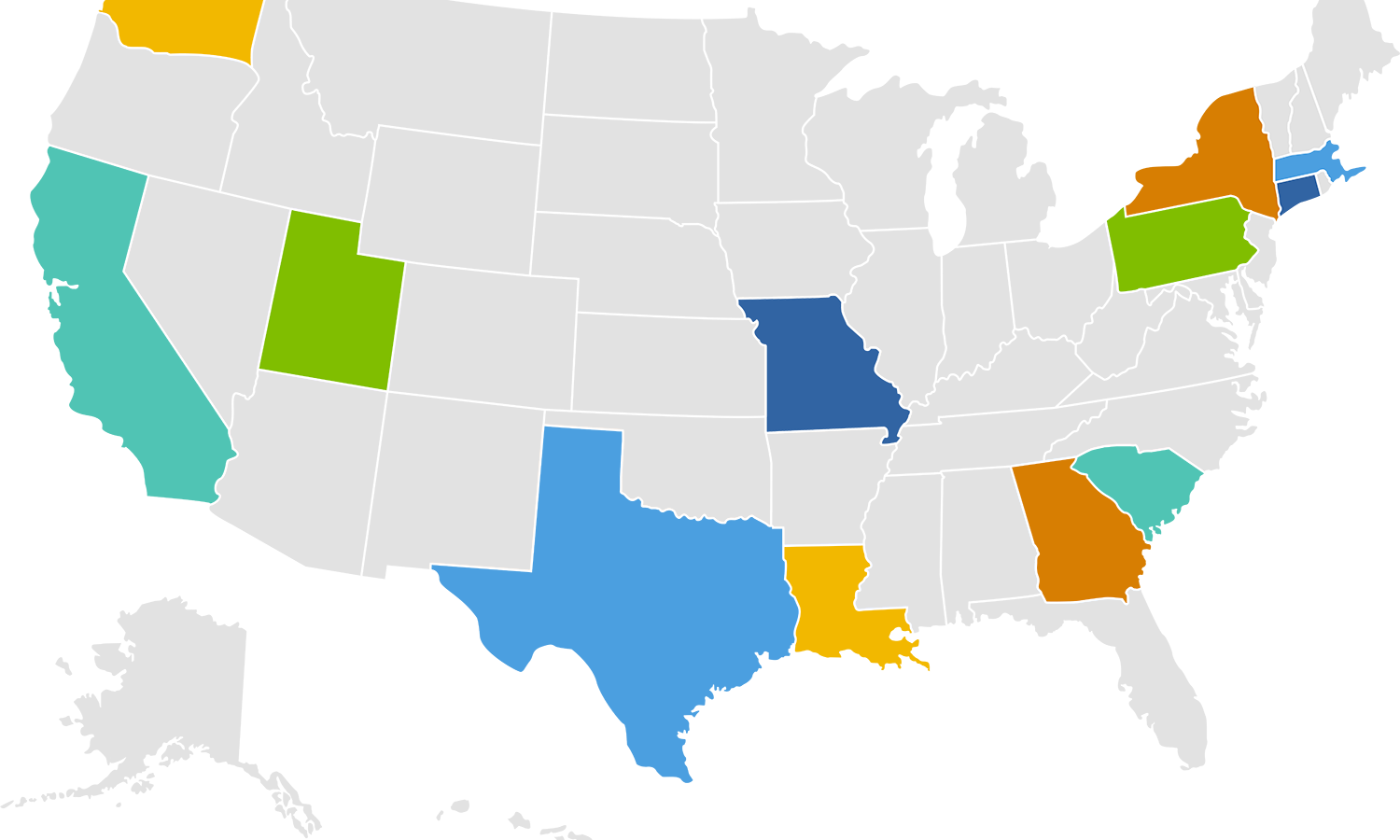
In May 2021, President Biden’s Executive Order on Improving the Nation’s Cybersecurity was announced. This executive order acknowledged the shortfalls of legacy systems, calling for public-private collaboration and cloud migration. Following this regulatory order, more than 36 states have enacted new regulations. For example, Texas passed State Bill 475 in 2021, designed to implement a standardized information security and risk program across all state agencies and their partners. For contractors doing work in any of these states, ensuring cyber compliance will become key to maintaining a steady flow of projects.